Nowadays, more and more businesses understand that digitalization is necessary for them to survive and thrive. A 2019 Deloitte Smart Factory study found that 86% of manufacturers felt their smart factory initiatives would be the main driver of competitiveness over the next five years. In 2020, these initiatives have been accelerated due to the global pandemic. In a recent report by the World Economic Forum, Building Resilience in Manufacturing and Supply Systems in the COVID-19 Context and Beyond, suggests that manufacturers adopt new working models and governing to increase manufacturing resilience. However, as we face the current crisis, accelerating digitalization alone is no longer sufficient. In this article, we will explore how to build resilient industrial networks and deploy cybersecurity defenses, in order to sustain continuous industrial operations.
As the number of cybersecurity incidents happening in industrial control systems (ICS) continues to increase, many organizations have started to develop their own cybersecurity strategies in order to protect assets they regard as critical to successful operations. “Is there a silver bullet that can address all vulnerabilities in the ICS?” Unfortunately, there is no such thing. Cybersecurity needs to be considered from different perspectives. The start of a cybersecurity journey often begins with a risk assessment. After this, companies can establish security policies accordingly. In order to implement the security policies, it is worthwhile to create a security architecture to help achieve secure network infrastructure. For instance, regulating who can access the network by utilizing access control lists. Finally, companies can proactively monitor and respond to cybersecurity incidents by implementing industrial cybersecurity countermeasures on OT networks.
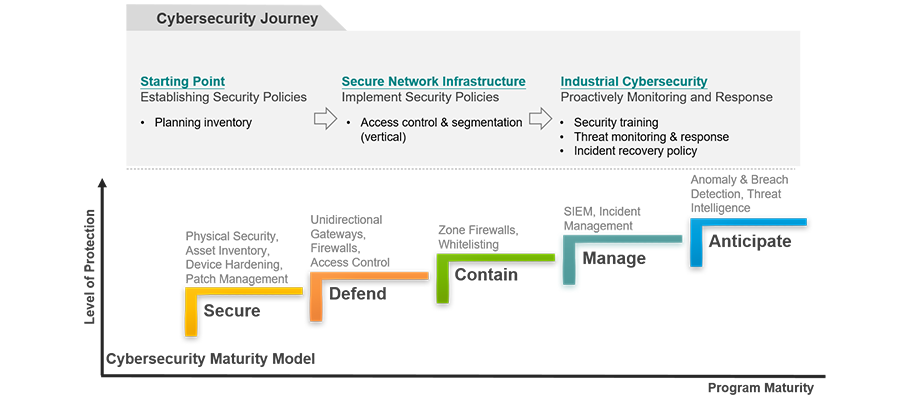
Diagram: A cybersecurity journey
Source: ARC Advisory Group, https://www.arcweb.com/industry-concepts/cybersecurity-maturity-model
As mentioned in the previous paragraph, every industrial cybersecurity journey includes different phases with relevant countermeasures. As there is no single solution that can cover all aspects, we recommend considering cybersecurity from a holistic perspective. Traditional countermeasures such as firewalls strengthen the perimeter defense of industrial networks. These provide effective vertical protection to prevent people who do not have permission to access the network. However, when someone manages to get through that defense or engineers accidentally dispatch a wrong command inside the network, there are no measures to mitigate the risks that can occur because of this. Therefore, deploying horizontal protection such as virtual patching and an IDS or IPS is also important. In the following sections, we will consider how vertical and horizontal protection both play a significant role on securing industrial networks.
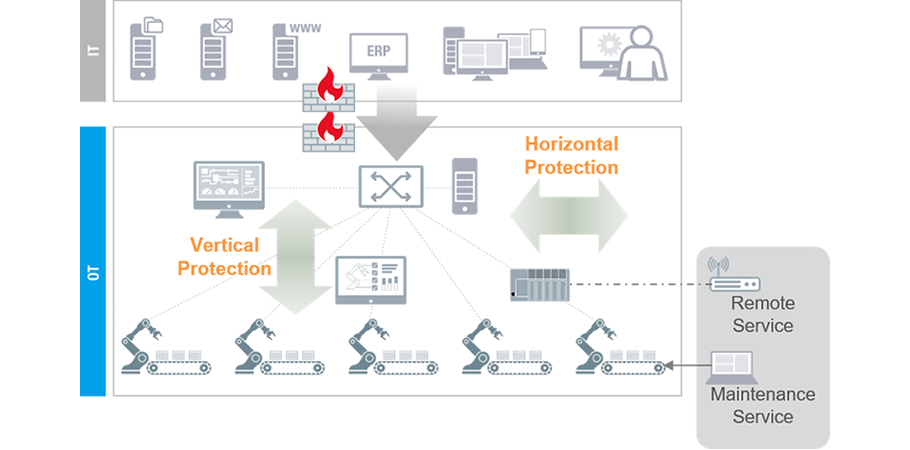 Diagram: Both horizontal and vertical traffic should be considered in order to create holistic cybersecurity countermeasures.
Diagram: Both horizontal and vertical traffic should be considered in order to create holistic cybersecurity countermeasures.
Network Management
Industrial networks have often been pieced together over years or even decades. Therefore, gaining visibility of the network and its various components and architecture can be a challenging first step. From our experience, we have discovered that an industrial network management tool that can scan a network and automatically draw out the topology will give OT engineers a lot of useful information, which in turn allows them to develop an action plan.
Network Protection
Network segmentation is a fundamental precaution that can ensure only certain traffic can flow within designated areas. There are several methods to achieve network segmentation. For instance, stateful firewalls can help create the first line of defense without needing to change the network topology, which is perceived as friendly for OT environments as they need to operate continuously. Creating virtual LANs (VLANs) within a larger network can also help segment networks. Another rule of thumb is to implement authentication via 802.1x (AAA/Radius TACACS) and access control via an ACL. Last but not least, remote control, monitoring, and maintenance have become more and more prevalent during an OT engineers’ daily operations. Therefore, it should always be remembered that ensuring secure remote access reduces the chance of breaches.
Device Security
As organizations start to take cybersecurity more seriously, the two biggest challenges include developing and implementing practical and appropriate security policies around authentication and network segmentation. Standards such as IEC 62443 can be very helpful in identifying policies that will make sense for their industrial networks. Download the white paper to learn more about IEC 62443.
As organizations start implementing cybersecurity measures into their industrial networks, the first step that is often taken to protect network traffic that travels vertically is a defense mechanism such as network segmentation. Is this sufficient? The answer, unfortunately, is no. Although north-south bound traffic is well managed and the defense is well built, employees, vendors, and contractors still have direct access to the networks. If there are no protection measures, this inadvertently allows them to bypass traditional protections such as firewalls and possibly introduce viruses or malware on to industrial networks. This is why horizontal protection such as virtual patching and intrusion prevention is crucial to protect critical assets such as PLCs and HMIs.
Industrial IPS Safeguards Critical Assets
Since PLCs and HMIs are designed to control production processes, if the communication between PLCs and the control center is compromised or HMIs malfunction, it could cause damage to assets or even personnel. Therefore, it is important to prevent any unauthorized protocols or functions going through PLCs and HMIs. An Industrial IPS (Intrusion Prevention System) features OT-centric Deep Packet Inspection technology, which can identify multiple industrial protocols and allow or block specific functions, such as read/write access. This way, you can be more confident that the traffic on your industrial networks is trusted and nonmalicious.
Virtual Patching Protects Unpatched Devices
It is a well-known rule to always keep devices updated in order to prevent any cyberthreats. However, in industrial networks, it is sometimes less ideal to stop the operations to perform the updates. Furthermore, updates may not be available for these critical assets. For instance, some HMIs are running on Windows XP, which no longer supports updates. Under such circumstances, virtual patches play an important role to safeguard critical assets from the latest cybersecurity threats.
Security Management Offers Clear Visibility
When a network is up and running, it can be quite a challenge to maintain and quickly adjust the network. Therefore, security management software is very helpful for managing devices and security policies, as well as performing virtual patches.
As there is no single cybersecurity solution, organizations have to examine their status and select the right combination of solutions. Try to think from both perspectives of secure network infrastructure and industrial cybersecurity to build vertical and horizontal protection.

Moxa combines industrial networking and cybersecurity expertise to provide layered protection for your industrial networks. Visit www.moxa.com/Security to learn more.

Be the first to learn about classes, training, webinars, products news and more.
We use only necessary cookies on this website to provide the best user experience and customer service.